MQTTLAB.IOTSIM.IO/aws
Portal for public SaaS MQTT labs based on
MIMIC MQTT Simulator
![]() with
Amazon AWS IoT Core
with
Amazon AWS IoT Core
![]() for AWS IoT training.
Check the listing on the
AWS Marketplace
for AWS IoT training.
Check the listing on the
AWS Marketplace
![]() .
.
You can try for free (no registration/credit card required) the other MQTT labs , then upgrade to this paid lab if you like it.
AWS IoT Get Started Tutorial
Overview
Onboarding an external device to AWS IoT for the first time is a task that until now took hours if not days. To overcome this hurdle, we created this AWS IoT Getting Started Lab to get started in minutes.
This MIMIC MQTT lab demonstrates integration of
Amazon AWS IoT Core
![]() and
MIMIC MQTT Simulator
and
MIMIC MQTT Simulator
![]() to produce an out-of-the-box lab for immediate first-time setup
and use of dynamically controllable
device shadows
to produce an out-of-the-box lab for immediate first-time setup
and use of dynamically controllable
device shadows
![]() .
By having a quick, successful example, you will short-circuit integration
of your own devices into AWS IoT.
.
By having a quick, successful example, you will short-circuit integration
of your own devices into AWS IoT.
Check out this 2-minute
Youtube video
![]() of simulated devices updating their device shadows in AWS IoT in
real-time.
of simulated devices updating their device shadows in AWS IoT in
real-time.
This lab sets up within 15 minutes a realistic third-party
MQTT-based sensor publishing JSON telemetry that fits the AWS IoT
device shadow
![]() guidelines.
There is no limit to the scalability, but we'll show 1 sensor setup
automatically using the AWS API, and then you can try the same yourself on any
number in the lab for your requirements (if you need more sensors,
send e-mail to sales@gambitcomm.com).
guidelines.
There is no limit to the scalability, but we'll show 1 sensor setup
automatically using the AWS API, and then you can try the same yourself on any
number in the lab for your requirements (if you need more sensors,
send e-mail to sales@gambitcomm.com).
Features
Features of this lab include:
- no prior requirements except for a valid AWS IoT Core account, ie. a
AWS IoT login
 . It's best if you know about the fundamentals of the Internet of Things
(IoT) and know the basics of AWS IoT, as detailed in their
training
. It's best if you know about the fundamentals of the Internet of Things
(IoT) and know the basics of AWS IoT, as detailed in their
training
 ;
;
- step-by-step instructions for all tasks;
- 1 realistic sensor (or more) that publishes telemetry via
MQTT
 ;
;
- the sensor is authorized to access your account (and only your account) in AWS IOT Core, just like real devices will have to be;
- dynamic telemetry published over the internet to AWS and reflected in the device shadow;
- real-time, interactive control of the telemetry to reproduce any scenario you want at any point in time;
- investigate all aspects of AWS IoT interaction with a third-party device;
- finally, verifiable cleanup of everything we setup automatically.
Tasks
These are the tutorial steps you are going to perform to get going quickly:
Do you have questions? Maybe we answered them in the FAQ below. If not, contact our support team.
The power of MIMIC is not limited to this. If you have a scenario you need simulated, send e-mail to sales@gambitcomm.com.
Step 1: Setup
Objective
Setup a temporary user in AWS for this lab. This guarantees that any outside access only goes through this temporary user. Later, when you remove the user, all further access will be denied.
This procedure is shown in this 3-minute
Youtube video
![]() .
You can follow along step-by-step by just pausing the video as needed.
.
You can follow along step-by-step by just pausing the video as needed.
Procedure
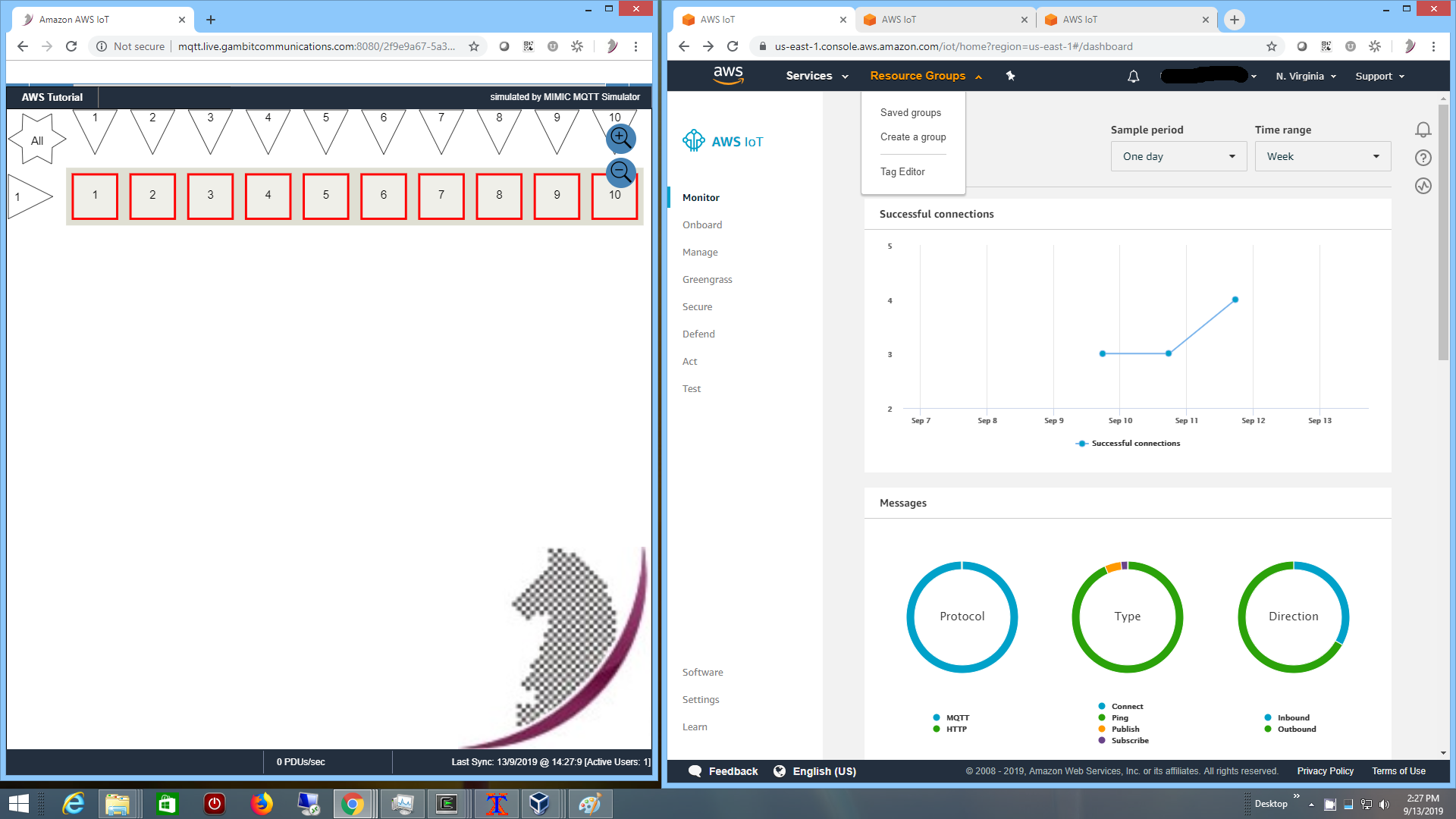
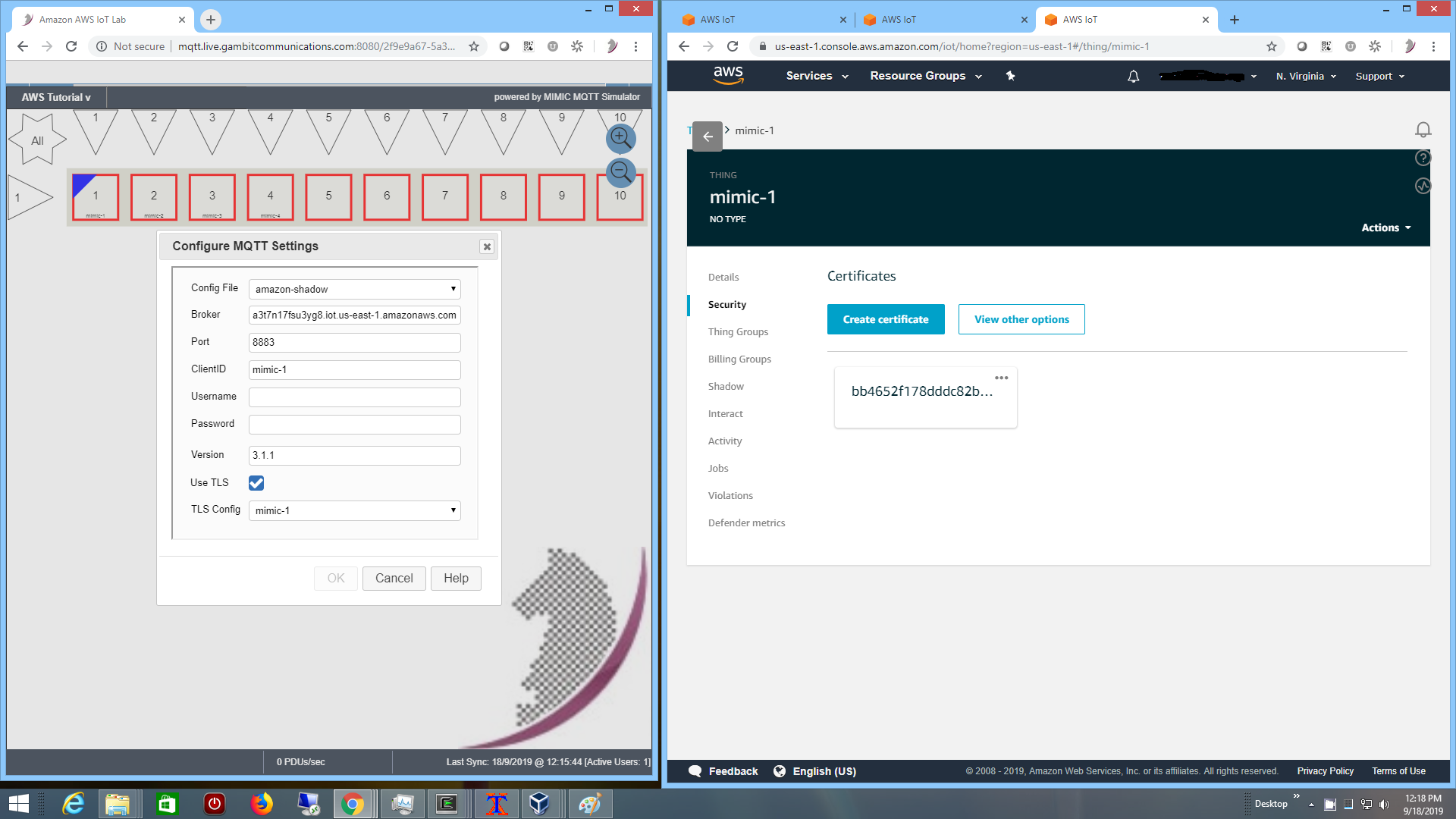
To setup your lab, we recommend 2 web browser windows side by side. For
example in the left browser window you can have your MIMIC MQTT lab for AWS,
and in the right your AWS console, logged into your
AWS IoT login
![]() , eg. as in Figure 1:
, eg. as in Figure 1:
Figure 1 - 2 browser windows side-by-side
You can maximize either of them when working in one window for a while.
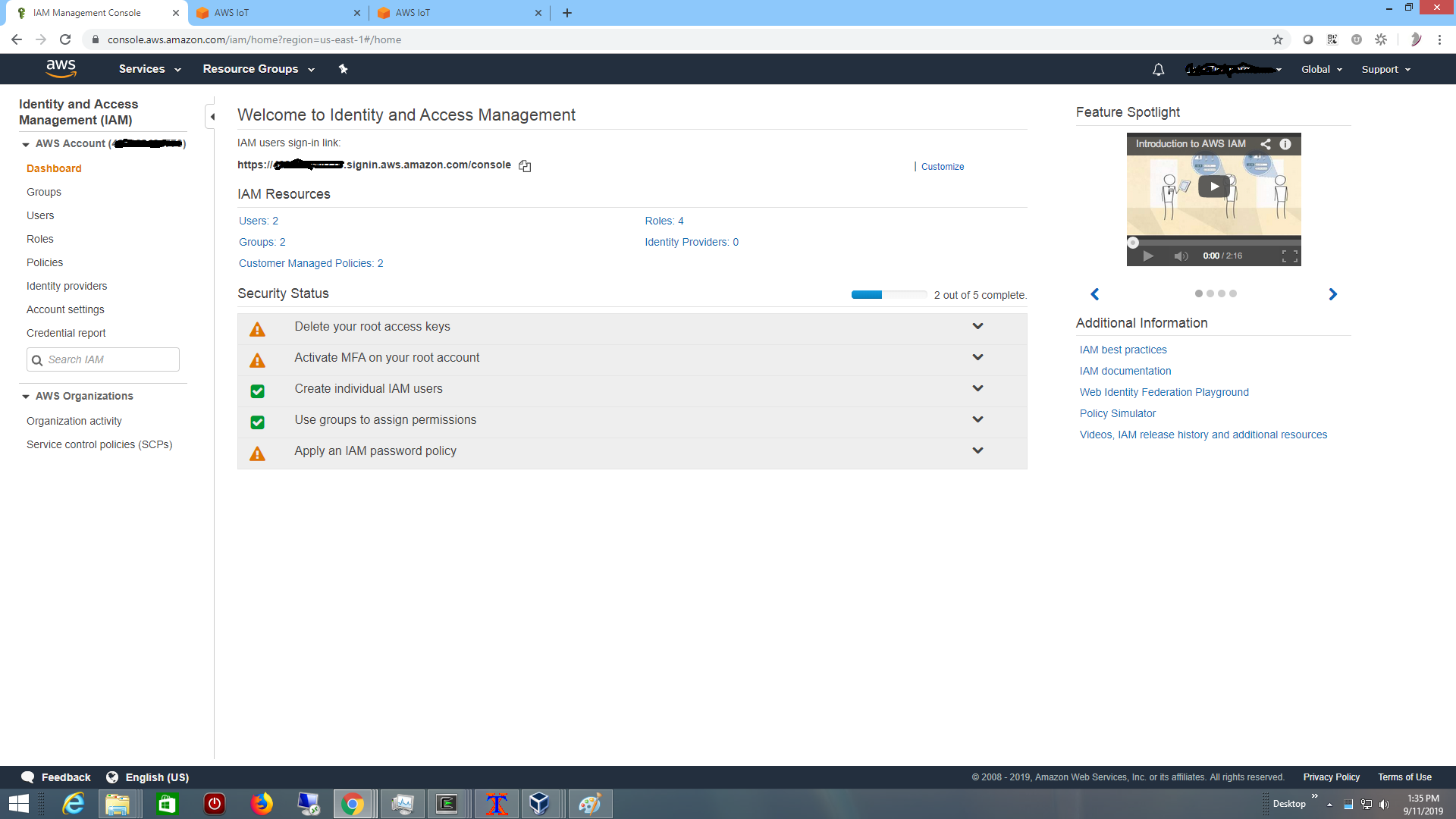
In the right browser window, in your AWS dashboard, just navigate to your
IAM Dashboard
![]() ie. pull down the top left Services and select IAM.
It should then say Identity and Access Management (IAM) in the
top left, as shown in Figure 2:
ie. pull down the top left Services and select IAM.
It should then say Identity and Access Management (IAM) in the
top left, as shown in Figure 2:
Figure 2 - AWS IAM console
First, you are going to create a temporary user for this tutorial. Everything in this tutorial will be done with that user, so once you are done, you can remove that user and you are sure no further access can occur. NOTE: this is the most complicated part of the tutorial, because we cannot automate it for you, and it shows you what is involved with AWS for when you have to do everything yourself.
-
Click on Users on the left menu, then Add User,
the Add user Set user details page appears.
-
The User name does not matter, we recommend
AWS_tutorial_user.
-
For Access type pick Programmatic access.
-
Then click on Next: Permissions at the bottom, and
the Set permissions page appears.
-
Pick Add user to group, then click on Create group.
-
In the Create group dialog, the Group name does not
matter, we recommend AWS_tutorial_group.
-
For Filter Policies type iot and it will find the
IoT-related policies. NOTE: click carefully here. Click the
checkbox in front of AWSIoTConfigAccess which will allow the
tutorial to configure things in your AWS account. Make sure the checkmark
appears before the name.
-
Then click Create group at the bottom.
-
It should go back to the Add User Set permissions page,
and the new AWS_tutorial_group should be selected. Click
Next: Tags at the bottom.
-
The Add User Add tags (optional) page appears.
We don't need any tags, so just click Next: Review at the bottom.
-
The Add User Review page appears, and when satisfied,
click Create user at the bottom.
-
A new Add User page appears with a green check mark and
Success. NOTE: this is important, because it is the only
place to get the Access key ID and Secret access key
for your new AWS user.
-
Copy/paste the access key and click on Show under
Secret access key and copy/paste it away for later (eg.
into a text file, or a Word document). These are the only 2 pieces of
information from your account to complete the AWS tutorial setup.
- Click Close and you are done with configuring your account for the tutorial.
In order to link this new temporary user between your AWS IoT and this lab, you will use the Step 1: Setup... menu item under the AWS Tutorial top menu.
-
Click on AWS Tutorial. then Step 1: Setup....
This will from now on be referred to as AWS Tutorial -> Step 1:
Setup.... The Step 1: Setup dialog appears.
-
Enter the AWS region that you want to have your IoT things to live
in, eg. the identifier after the region= in your AWS
console. Eg. if your AWS console is at
https://console.aws.amazon.com/iot/home?region=us-east-1#/dashboard
you would enter us-east-1.
-
Copy/paste the access key ID and secret access key from above into
each the respective fields in the dialog, then press OK.
- Once you click OK, a new Run Script Console tab is opened in the browser with the output of the processing. When it says Task completed, and there are no ERROR messages, your lab is configured to work with your AWS account.
Results
The temporary user is setup and you are ready to use the MIMIC MQTT Lab to add a device, investigate how it connects, and play with it.
Step 2: Add Device(s)
Objective
The left MIMIC MQTT lab browser window shows red icons, one for each simulated device. This is the equivalent of your real-world devices sitting on your lab bench. They are not doing anything.
We need to configure one of the devices to publish telemetry to AWS
IoT Core. This task configures AWS IoT to allow access by the device,
similar to the manual procedure outlined at
this page
![]() ,
and configures the devices to use the access keys provided by AWS IoT.
,
and configures the devices to use the access keys provided by AWS IoT.
Procedure
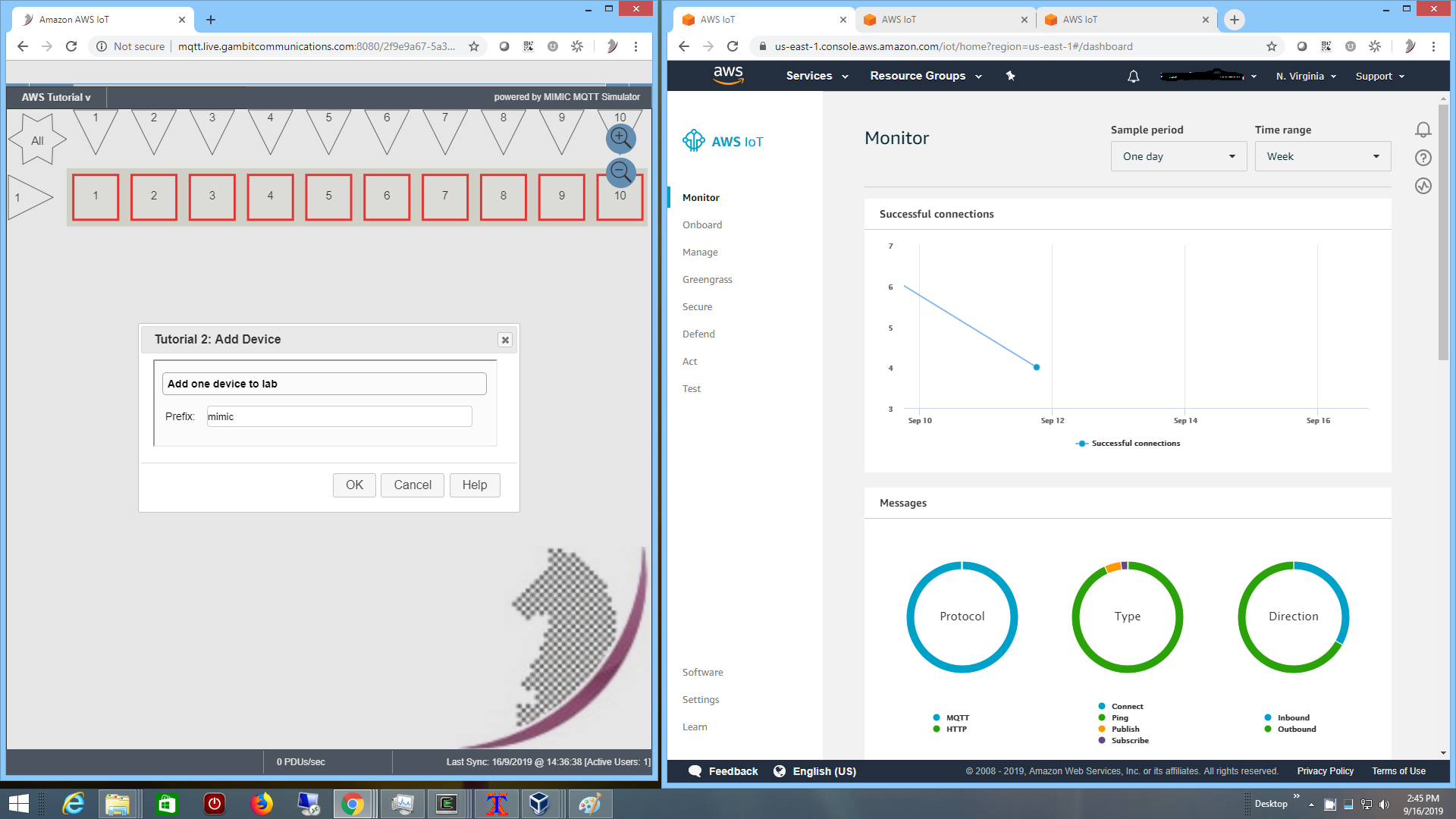
Click on AWS Tutorial -> Step 2: Add Device.... The Step 2: Add Device dialog appears.
Figure 3 - Step 2: Add Device dialog
Type the Prefix for the thingName of the thing to be created in your AWS account. We recommend to keep mimic, that way you can find it easily later. The first thingName will be mimic-1.
Once you click OK, a new Run Script Console tab is opened in the browser with the output of the processing. When it says Task completed, and there are no ERROR messages, your new sensor device is added to your AWS account and integrated with the MIMIC MQTT Lab. You can dismiss this tab, or switch back to the lab browser tab titled Amazon AWS IoT Lab.
If it does not have it already, when you now reload the MIMIC MQTT Lab window, the first icon should have a name underneath its number, eg. the first device will be named mimic-1. It is red because it is currently stopped. This is the equivalent of the device sitting on your lab bench in the real world with power switched off.
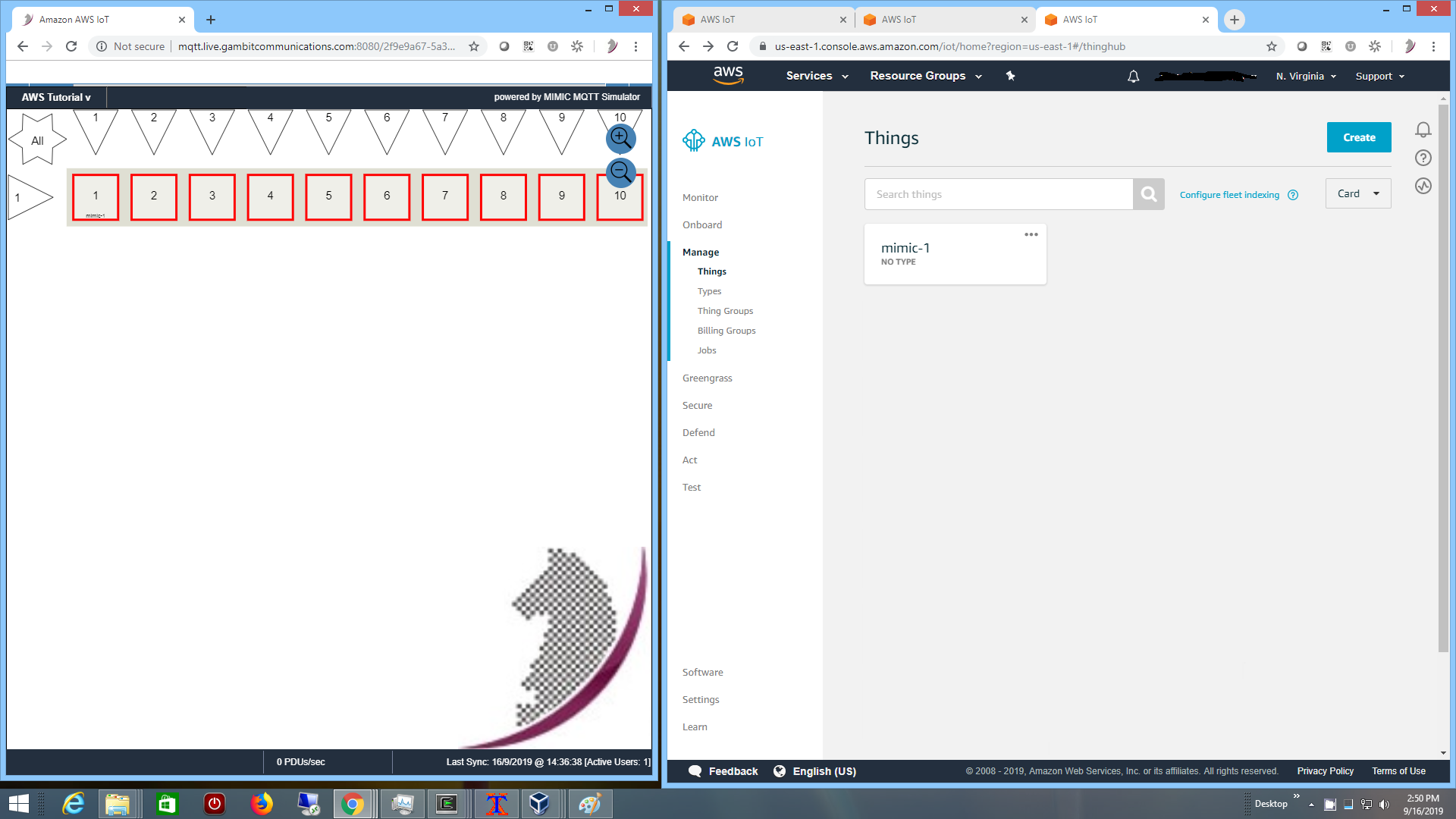
Also, in your
AWS IoT Console
![]() ,
under the Manage menu click Things and you will see
the newly created thing:
,
under the Manage menu click Things and you will see
the newly created thing:
Figure 4 - Step 2: Thing in AWS IoT
NOTE: The new things are created in the region you selected in the Setup step above eg. us-east-1, and will not show if you navigate to a different region, eg. us-east-2.
Results
We did the following in AWS IoT:
-
created a thing with thingName mimic-1;
-
created a certificate for the thing to access AWS IoT over SSL;
-
created a policy AWS_tutorial_policy to allow IoT operations;
- linked the three
You can click on the thing in your AWS IoT Console and investigate its settings. You are now ready to experiment with this thing in the next sections.
Using the lab
To start using the lab, first verify that at least one thing with the chosen
prefix, eg. mimic-1, is showing in your
AWS IoT Console
![]() as shown in Figure 4 above.
as shown in Figure 4 above.
Step 3: Start Device(s)
Objective
The devices in your lab are stopped, equivalent to lab equipment sitting on your lab bench and powered off. So they are not doing anything. We need to power up the recently configured device, the one that is labelled mimic-1.
Procedure
To start it, select the red icon(s) of the device(s) you want to start. Each selected device will have a blue triangle in the upper left. Then click on AWS Tutorial -> Step 3: Start Device(s) -> Go!.
The selected icon(s) will turn green, as if you had turned power on.
Just like the equipment on your lab bench, whether it delivers telemetry to AWS IoT or not depends on whether you have configured the correct parameters in the MQTT client software.
In this lab, if you added the device as in the section above and there were no errors, then it will publish telemetry once a second. You will know that it works when a orange <--> arrow appears in the icon, indicating activity.
In your AWS Iot Console, you can click on the thing that you started, then go to its Shadow, and telemetry will be updating. In particular, we made it so that the light value changes frequently at random, like a flickering light.
Results
The icon of the selected device shows green to indicate that it is started, and telemetry is published to AWS IoT. Now you can investigate further how things work, and change telemetry on the fly.
Step 4: Investigate
Objective
Now that it is running, you'll want to see how the lab device and your AWS IoT Thing are linked. That way you can reproduce this with your real devices.
Procedure
To check the configuration of the device in your AWS IoT Console,
click on the Thing, and then click Security on the left.
It shows the certificate for SSL communications, when you click
on it, it shows the AWS_tutorial_policy policy attached
to it. Those determine how your MQTT device can
interact with AWS IoT Core
![]() .
.
To check the configuration of the simulated device in MIMIC, select the device icon in the lab, then click on AWS Tutorial -> Step 4: Investigate -> MQTT Configuration...
Figure 5 - Step 4: MQTT Configuration
The important configuration parameters for the device are the
-
Config File - this defines the MIMIC simulation: what MQTT payload
to send where and when. Here we publish once a second the telemetry to
the device shadow topic with a JSON message containing:
{ "state" : { "reported" : { "color" : COLOR, "power" : "on", "mem": MEMORY, "light": LIGHT, "temp": TEMP } } }The COLOR value is assigned at random at device start, simulating attributes that are determined at device startup.
The MEMORY value increments sequentially, like an incrementing resource value.
The LIGHT value changes at random for this tutorial. This simulates a very dynamic attribute that changes at every sample.
Finally, the TEMP values can be dynamically controlled to achieve on-demand, consistent, real-time results, eg. in the Step 5: Change Telemetry section below.
-
Broker - your AWS IoT::Data endpoint as detailed in the
Developer Guide
 and shown in the left-hand Settings menu item in your
AWS IoT Console.
and shown in the left-hand Settings menu item in your
AWS IoT Console.
-
Port - 8883 for secure MQTT communications
-
ClientID - set to the thingName
- TLS Config - uses the certificates assigned to the thing by AWS IoT
These are the configurables you would have to setup in your real-world device to communicate with AWS IoT.
NOTE: The OK button is disabled in this lab. More advanced labs allow you to configure anything on the simulated devices.
You can investigate the TLS certificates with Step 4: Investigate -> TLS Configuration...
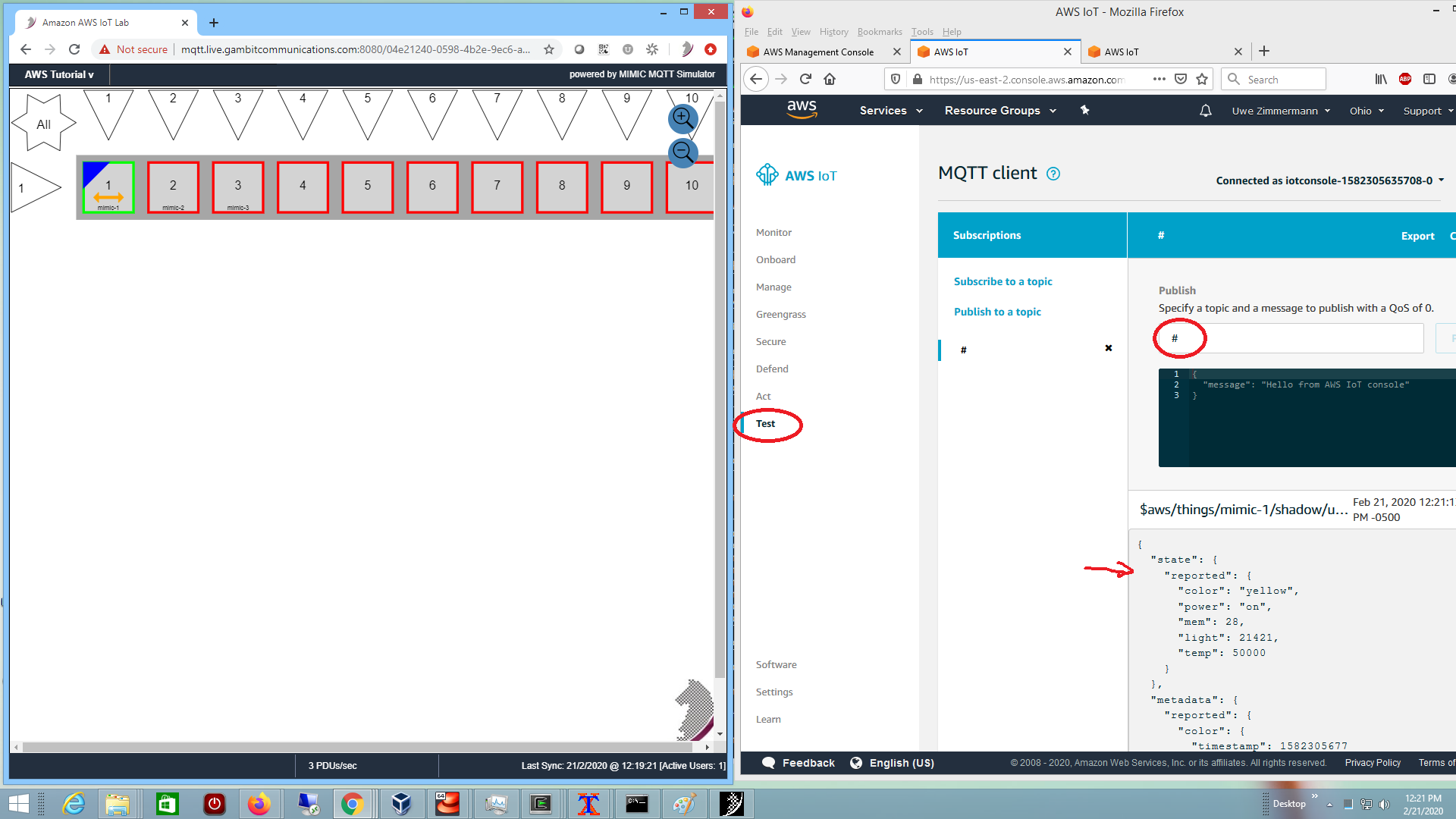
To check the messages received from the simulated device, you can use the left-hand Test menu item in your AWS IoT Console. Pick Subscribe to a topic, and in the Subscription topic entry enter # (the wildcard topic). Once you click Subscribe... you will receive the messages published by the devices in your lab.
Figure 6 - Step 4: Check received messages
Results
We verified the necessary configuration for a device to communicate with AWS Iot Core. We saw the topics and payload of the messages published by the simulated device.
Step 5: Change Telemetry
Objective
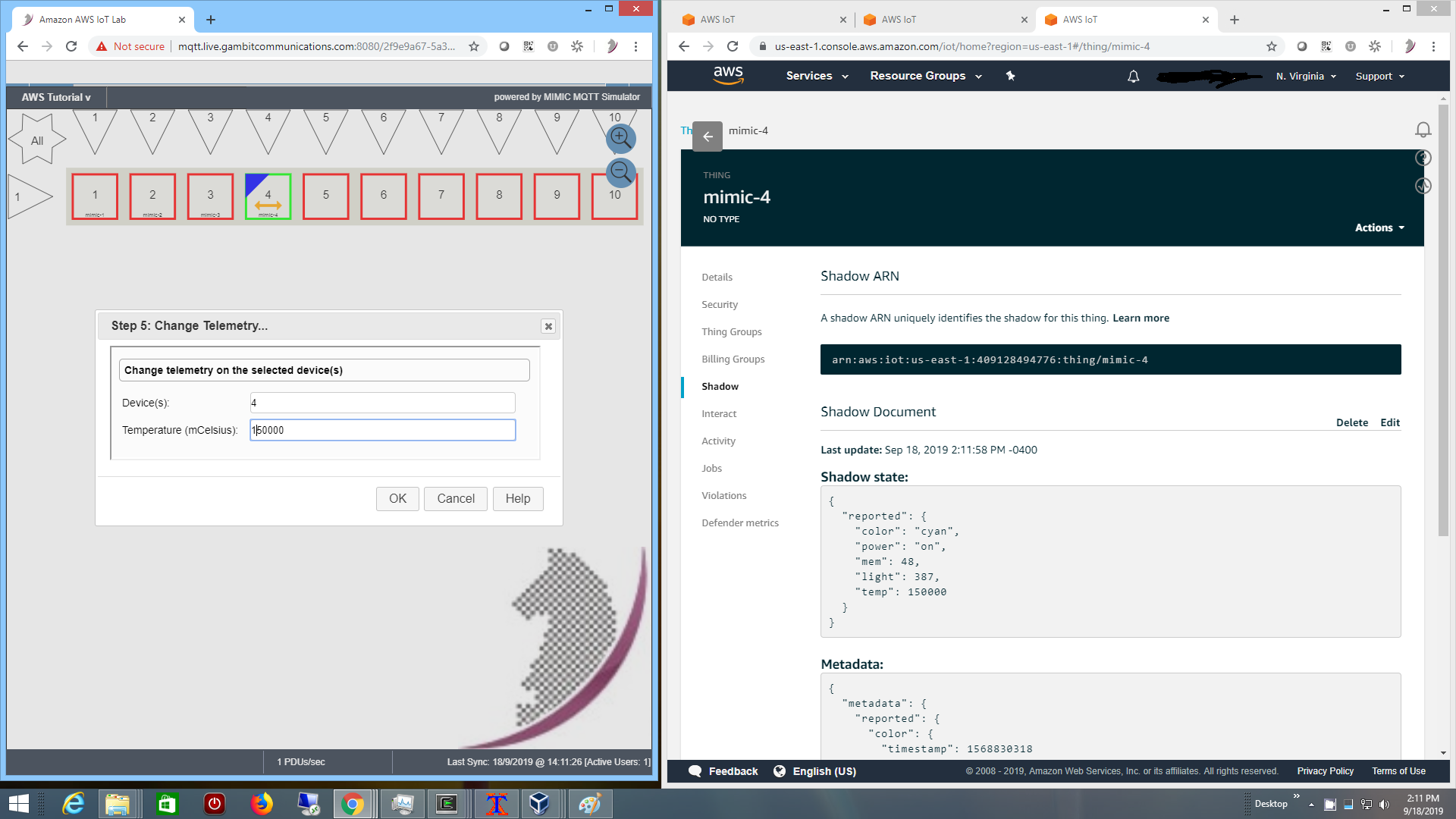
You are seeing real-time, dynamic telemetry in your device shadow on AWS IoT. The temp value is static, while the light value changes at random, like a flickering light. In this task we will interactively change the temperature to some other predictable value. This lets you change the temperature on-demand, eg. a device over-heating. Imagine the effort to do this with a real device.
Procedure
If you have not done so already above, in the MIMIC lab window select the icon(s) of the device(s) you want to manipulate and start it. Each selected device will have a green icon and a blue triangle in the upper left. Then click on AWS Tutorial -> Step 5: Change Telemetry....
In the Step 5: Change Telemetry dialog, change the Temperature value to something else, eg. 80000. As soon as you click OK, the new temperature value is published.
Figure 7 - Step 5: Change Telemetry
In your AWS Iot Console, you can click on the thing that you started, then go to its Shadow, and the new temp telemetry will be reflected.
Results
We changed temperature telemetry on the fly, on-demand, predictably. You can use this technique when it comes to testing your application for certain conditions.
Step 6: Stop Device(s)
Objective
Your lab devices are continuously generating telemetry and publishing messages to AWS IoT Core. This task stops them, the equivalent of powering down the real equipment.
Procedure
In the MIMIC lab window select the icon(s) of the device(s) you want to stop. Each selected device will have a blue triangle in the upper left. Then click on AWS Tutorial -> Step 6: Stop Device(s).
The icon(s) will turn red, and messages cease to be published.
Results
We stopped the devices to stop publishing messages.
Step 7: Optional Tasks
These are further optional, advanced tasks you can do in your lab:
-
repeatedly do
Step 2: Add Device
, and it will add more things with incrementing instance number upto
the total allowed in your lab. Once you start the lab devices,
you will see independent telemetry for each;
-
create a thing in AWS IoT console as detailed at
this page
 .
.
-
edit a thing to add it to a
thing group
 to manage collections of your things;
to manage collections of your things;
-
add a
thing type
 and apply it to your thing in order to constrain and categorize it;
and apply it to your thing in order to constrain and categorize it;
-
add rules to take actions with received messages on device shadow
updates as outlined in their
AWS IoT Rules Tutorials
 :
:
-
Graph real-time telemetry with
AWS Cloudwatch
 as shown in this
3-minute video
as shown in this
3-minute video

-
This
3-minute video
 demonstrates archiving of the sensor messages in a
DynamoDB
demonstrates archiving of the sensor messages in a
DynamoDB
 table.
table.
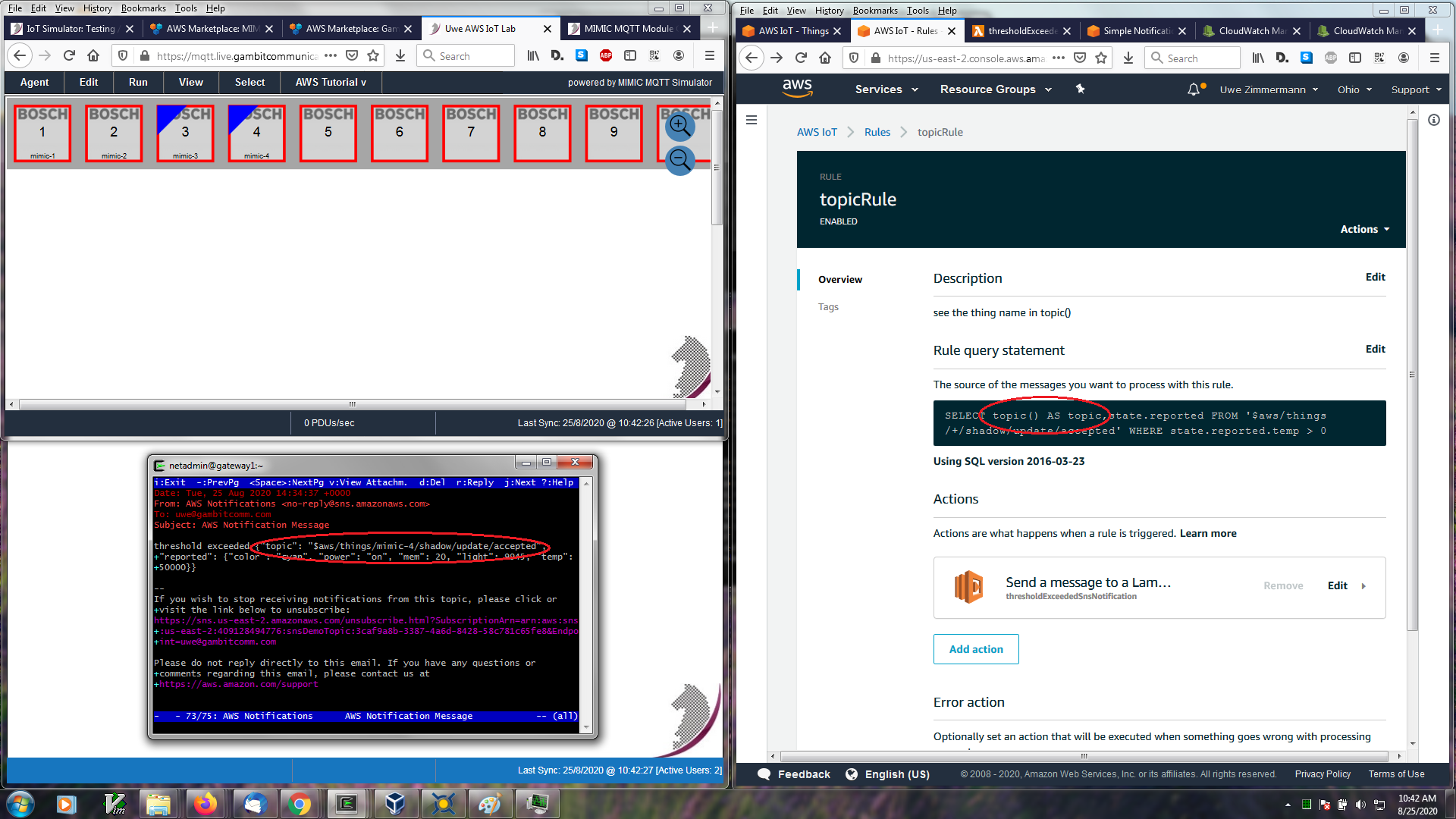
-
In this
2-minute video
 we test multiple Lambda functions for different thresholds,
generating e-mail notifications via the SNS service.
we test multiple Lambda functions for different thresholds,
generating e-mail notifications via the SNS service.
-
we added the topic to the rule so that multiple devices have unique
notifications as shown in this screenshot:
Figure 8 - Step 7: Thing ID in SNS notifications
-
Graph real-time telemetry with
AWS Cloudwatch
-
explore the
Basic Ingest
 feature to reduce messaging costs as shown in this
2-minute video
feature to reduce messaging costs as shown in this
2-minute video
 .
.
-
use the
AWS APIs
 to automate tasks related to your AWS IoT deployment. For some
open-source scripts, see
our Github code
to automate tasks related to your AWS IoT deployment. For some
open-source scripts, see
our Github code
 .
.
-
explore how you will implement your IoT application to follow the
AWS Well-Architected Framework
 ,
,
-
write your first application that acts on telemetry of your sensors,
eg. start with our open-source
monitor-thresh subscriber client
,
in particular this
2-minute video
 ,
,
-
integrate with other IoT platforms to visualize and act on telemetry, such
as with
-
Ubidots
 ,
in this
3-minute video
,
in this
3-minute video
 ,
or with
,
or with
-
TagoIO
 ,
in this
2-minute video
,
in this
2-minute video
 .
.
-
Ubidots
Step 8: Cleanup
Objective
Once a lab is setup, you want to clean it up when you are done, to be certain no left-over devices have access to your account. This procedure makes certain there are no left-overs.
Procedure
The AWS Tutorial -> Step 8: Cleanup... lets you cleanup devices setup in the lab. Just select the device(s), then that menu item cleans up any associated resources from both AWS IoT and the MIMIC MQTT Lab.
Once you have deleted a device, you can add one back in with different credentials with the Add step above.
To clear the rest, as detailed for Q: What about security / privacy? in the next section, ie.:
-
remove the AWS_tutorial_policy in your AWS IoT Console under
Secure and Policies.
- remove the AWS_tutorial_user in your AWS IAM Dashboard that you used in the Setup step above. Once you do this, you no further operations will work in this lab until you setup again with a new temporary user.
Frequently Asked Questions
- Q: What will this cost me?
A: If you are renting through the AWS Marketplace
 ,
the costs are indicated there. Else, if you are renting directly from
Gambit,
besides the fixed cost for the MIMIC MQTT lab, there will be minor
AWS IoT costs
,
the costs are indicated there. Else, if you are renting directly from
Gambit,
besides the fixed cost for the MIMIC MQTT lab, there will be minor
AWS IoT costs
 in your Amazon account that we cannot control, most likely less than
$1. Well worth the savings in effort in seeing a third-party device
publish to the AWS IoT device shadow in under 5 minutes.
in your Amazon account that we cannot control, most likely less than
$1. Well worth the savings in effort in seeing a third-party device
publish to the AWS IoT device shadow in under 5 minutes.
IMPORTANT: if you are using this lab through AWS, make sure to terminate any instances that you launched, as they WILL incur charges if left running.
- Q: What exactly does this do to my AWS account?
A: You setup a temporary user AWS_tutorial_user and group AWS_tutorial_group in the above Setup.
If you run the Step 2 - Add dialog with your AWS authentication parameters it will setup exactly 1 device instance with an associated certificate that links to the AWS_tutorial_policy policy. Any subsequent device additions create a new certificate and thing that link to that policy.
If you try some of the optional investigations in Step 7 - Optional Tasks above, then additional resources will be allocated in AWS that you need to cleanup.
- Q: What about security / privacy?
A: The lab will be able to access your account during the session because access tokens are stored in the lab configuration. You can delete the temporary user AWS_tutorial_user and policy AWS_tutorial_policy that you created in the Setup section above. Then you can verify that the devices can no longer talk to your account. This is verifiable cleanup, ie. you have proven that the outside device cannot access any more.
- Q: What next?
A: This lab gives you a small successful step in connecting a few third-party sensors publishing real-time, dynamic, predictable, controllable telemetry to AWS IoT Core device shadows in a matter of minutes. The next steps are up to you:
- You can build on what you learned to connect your own devices to
AWS IoT Core;
-
Explore our other free resources / videos to learn about solutions to
common problems you will encounter in IoT development;
-
You can rent a lab anytime you need to test different aspects of your
application, or lease a longer-term
MIMIC MQTT Simulator
 with more features;
with more features;
- You can scale the deployment to as many devices as you need to test, demo, train your IoT Application.
- You can build on what you learned to connect your own devices to
AWS IoT Core;